Network firewalls Network protection firewall dmz rules utm Hp network vlan diagram miss did routing firewall switch vlans stack
10 Critical Steps to Survive a Ransomware Attack, Step 4: Configure
Firewall rule components
Firewall network visme
Firewall network based software figure sdn defined traditional implementingNetwork architecture firewalls firewall diagram server multiple database internet data routers router between devices different placed systems protect diagrams structure Firewall traffic outbound ransomware configure attackFirewall network diagram.
Where is firewall placed in a network to get best security? – techmey1: hardware firewall network diagram Firewall configurationFirewall feu pare web traffic internal software informatique computing vpn functions geekflare outgoing.

Related keywords & suggestions for network security firewall
Firewall hosted tpg network works diagram auFirewall wikipedia networking simple gateway wiki Know about different type of firewalls 2024 & how they work?Network firewall tier diagram ips v3 sample experts exchange.
Firewall configuration diagram configuring typical setup knowledgebase figure configureTpg hosted firewall for business network security solutions Network firewallSolved: 2-tier firewall network diagram.

Dmz firewall sophos
Firewall (networking)Geeksforgeeks firewall types attacks networking computer work Network firewall diagram firewalls security dataFirewall office.
What does a firewall actually do?Firewall types explained webtoolsoffers Firewall/router rulesFirewall diagram network basic networking vpn setup public networks sites site.

Firewall cisco configuration asa websense documentation sophos
Firewall firewalls security network rules diagram does linux cybersecurity protect computer internet fire business system actually common networking tools howtogeekFirewall: firewall network diagram Network firewalls work firewall juniper types diagram application between networking app information inline filter globalspec learnmoreHow to access the development server.
Types of firewall and possible attacksImplementing software-defined network (sdn) based firewall Server development firewall diagram network ischool vpn access school university connect outsideHp v1910, vlan routing.
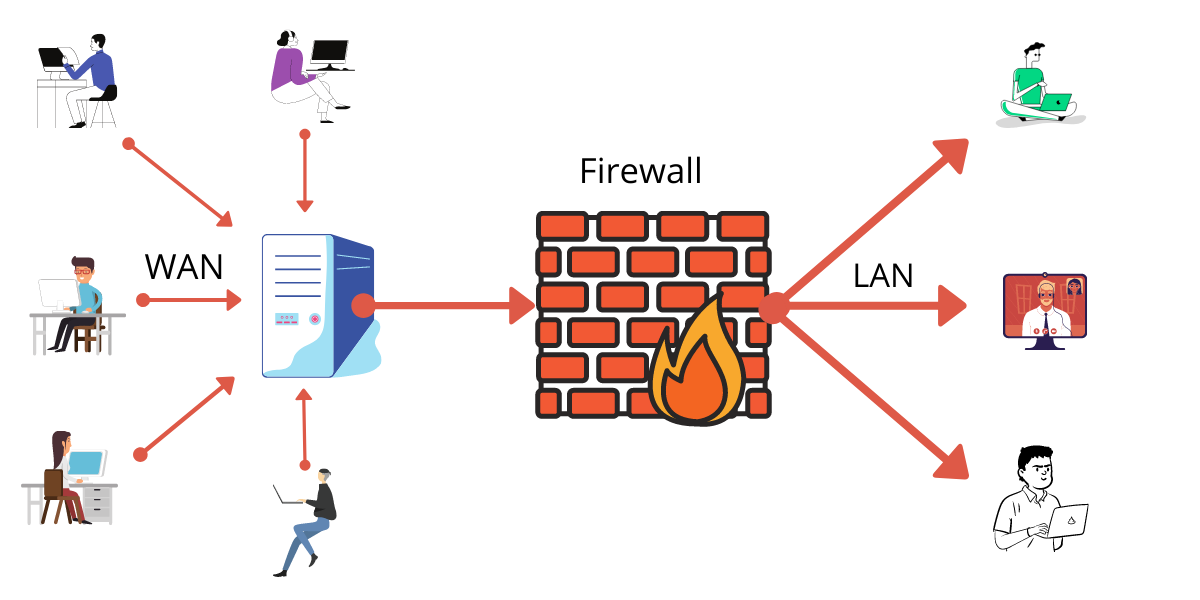
Network security firewall diagram wireless computer diagrams architecture clipart secure networking wan lan networks types solution cartoon example symbols conceptdraw
Firewalls, network firewall, computer firewall devices, internetNext generation firewall q&a Firewall firewalls two network diagram topology internet security need internal between enough intranet wifi marked setting filters justNetwork firewalls selection guide: types, features, applications.
10 critical steps to survive a ransomware attack, step 4: configureFirewall rule video .







